Code obfuscation
How JavaScript obfuscation enhances app security
A short introduction to JavaScript Software and apps based on JavaScript (JS) are everywhere now, and that’s why it’s more important than ever to consider JavaScript obfuscation. JavaScript is currently the most popular programming language and has the highest number of contributors and repositories, outpacing other alternative programming frameworks. Hybrid mobile app frameworks such as; React Native […]
A short introduction to JavaScript
Software and apps based on JavaScript (JS) are everywhere now, and that’s why it’s more important than ever to consider JavaScript obfuscation. JavaScript is currently the most popular programming language and has the highest number of contributors and repositories, outpacing other alternative programming frameworks.
Hybrid mobile app frameworks such as; React Native and Cordova make life easier for developers as they can write code once and build apps that run on the leading mobile OSs with no extra effort. The app will run on Android and iOS, and the code can be reused for PWAs (progressive web applications).
JavaScript Obfuscation – Why do you need it?
Developing a single hybrid app is quicker and may be more cost-effective than developing native Android and iOS individually. However, hybrid apps can be more vulnerable to attacks than apps written using native languages because JavaScript is easier to reverse engineer and modify as it is not compiled into a more abstract representation in the published app.
Unprotected JavaScript code increases the risk of exposing your businesses to IP theft, loss of revenue, or reputation damage. Therefore, it’s not enough to design apps with security in mind — app providers must actively protect their apps against emerging threats with a strong layer of defense to safeguard critical JS code from attackers.
What are the consequences?
- Your code can be copied and used without permission
- It makes your code vulnerable to hackers
- Your app’s functional logic on the client-side and algorithms are exposed.
The advantages of JavaScript Obfuscation
JS obfuscation is a series of code transformations that turn exposed code into a modified version that is hard to understand and reverse-engineer. This way, you ensure that your product’s intellectual property is protected against security threats, the discovery of app vulnerabilities, and unauthorized access.
When your app’s code is obfuscated, an attacker’s threshold to carry out a reverse engineer-attack is significantly increased, as it will often be too time-consuming and costly to succeed.
How to protect your JavaScript apps
Choose app security software that applies robust JavaScript obfuscation techniques to your apps. While code obfuscation makes your business less prone to reverse engineering and intellectual property theft, you should not solely rely upon obfuscation as it does not protect your apps from malware or real-world attack scenarios. Therefore, complete code protection combined with comprehensive runtime protection is essential to protect your JavaScript apps fully.
Obfuscation techniques
The main objective of obfuscating your JavaScript code is to hide the parts of the code that attackers could target by hiding things like strings, objects, and variables. Essentially, obfuscation makes it hard to analyze your code to conceal the meaning of the data. In general, JavaScript obfuscation revolves predominantly around adding entropy – or complexity – to the JavaScript, to make it more difficult to understand.
Script before JavaScipt obfuscation
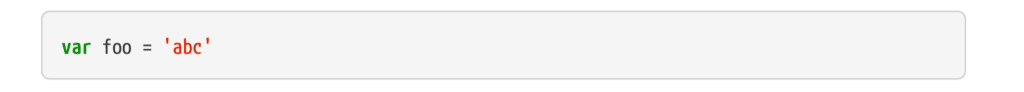
With a series of code transformations, your exposed script is made more difficult to analyze, understand and reverse engineer.
Combine JavaScript obfuscation with multi-layered runtime protection
Developers should strongly consider utilizing JavaScript obfuscation in combination with multi-layered runtime app protection, particularly if those apps run in an untrusted environment (Operating System).
By adding runtime protection to your app, your app can detect and protect against tampering or malware attacks. Sophisticated mobile malware exploits various security vulnerabilities in the mobile OS and uses diverse techniques to achieve its key goals. For example, Malware can misuse the Android Accessibility APIs to attack your app.
Anti-tamper controls also make your app able to detect emulators/debuggers and tampering attempts and prevent attackers from analyzing or modifying your code at runtime. The technique checks its own code to ensure the app is in its original state, and if attackers are using malware or code tampering software to enter the app, runtime protection techniques will detect and block it.
How Promon SHIELD™ protects your JavaScript apps
In addition to applying robust obfuscation techniques to your JavaScript apps, our app shielding solution will also monitor your app’s runtime behavior and detect if your app executes in an insecure environment. Promon SHIELD™ also detects the presence of code hooks, blocks injection of malicious code into the app, and enables your app to modify its behavior in real-time to interrupt potential malware attacks.
Utilizing code obfuscation combined with a multi-layered app shielding solution will make your apps less prone to reverse engineering and intellectual property theft.