StrandHogg 2.0 – The ‘evil twin’
Promon researchers have discovered a new elevation of privilege vulnerability in Android that allows hackers to gain access to almost all apps.
Classified ‘critical severity’ (CVE-2020-0096) by Google, the vulnerability has been named StrandHogg 2.0 by Promon due to its similarities with the infamous StrandHogg vulnerability discovered by the company in 2019.
While StrandHogg 2.0 also enables hackers to hijack nearly any app, it allows for broader attacks and is much more difficult to detect, making it, in effect, its predecessor’s ‘evil twin’.
Having learned from StrandHogg and subsequently evolved, StrandHogg 2.0 doesn’t exploit the Android control setting ‘TaskAffinity’, which hijacks Android’s multitasking feature and, as a result, leaves behind traceable markers.
Download this report for more details and get the mitigation recommendations
Instead, Strandhogg 2.0 is executed through reflection, allowing malicious apps to freely assume the identity of legitimate apps while also remaining completely hidden.
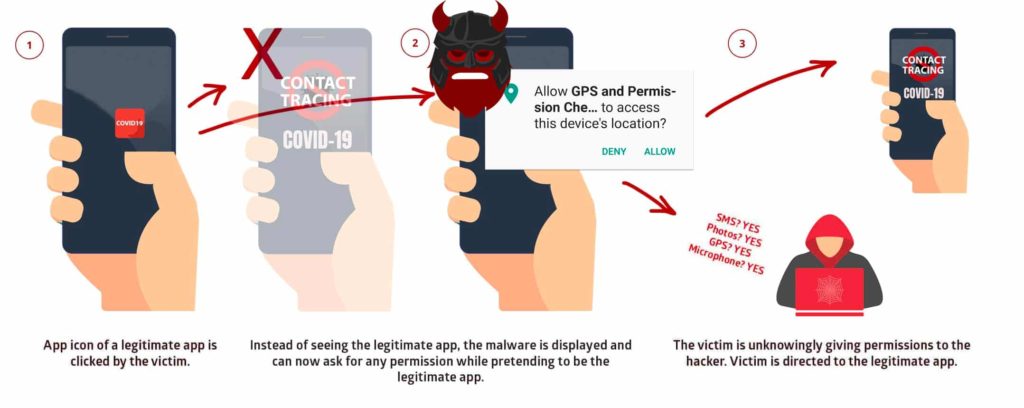
Utilising StrandHogg 2.0, attackers can, once a malicious app is installed on the device, gain access to private SMS messages and photos, steal victims’ login credentials, track GPS movements, make and/or record phone conversations, and spy through a phone’s camera and microphone.
StrandHogg 2.0 vs StrandHogg
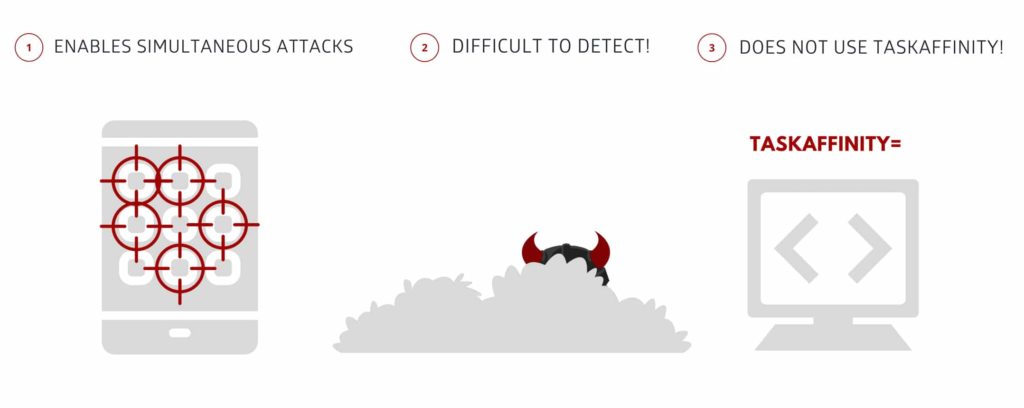
StrandHogg 2.0, being the more cunning twin, has learned how to, with the correct per-app tailored assets, dynamically attack nearly any app on a given device simultaneously at the touch of a button, unlike StrandHogg which can only attack apps one at a time.
As a result, StrandHogg 2.0 broadens its attack capabilities significantly! Like its predecessor, StrandHogg 2.0 doesn’t require root access or any permissions from the device in order to be executed.
Just like its relatively less evil twin, StrandHogg 2.0 is extremely dangerous because it enables sophisticated attacks, even on unrooted devices.
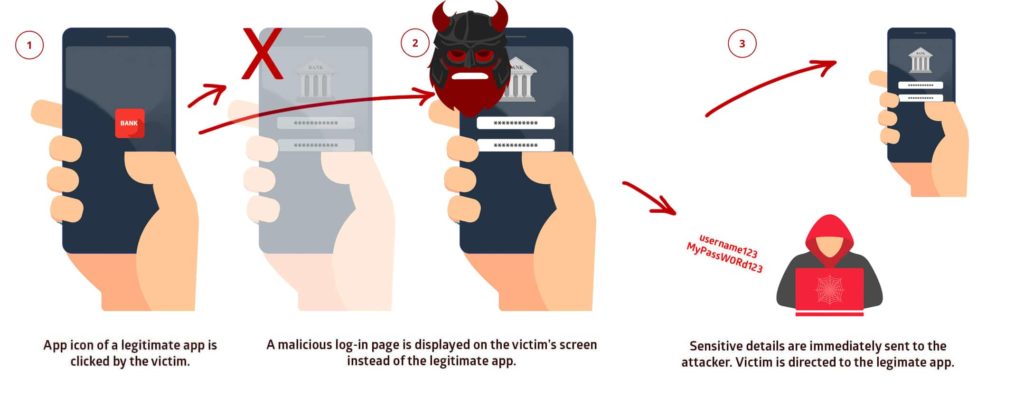
By exploiting this vulnerability, a malicious app installed on a device can attack and trick the user so that when the app icon of a legitimate app is clicked, a malicious version is instead displayed on the user’s screen.
If the victim then inputs their login credentials within this interface, those sensitive details are immediately sent to the attacker, who can then login to, and control, security-sensitive apps.
StrandHogg 2.0 is also much more difficult to detect because of its code-based execution.
Attackers exploiting StrandHogg have to explicitly and manually enter the apps they are targeting into Android Manifest, with this information then becoming visible within an XML file which contains a declaration of permissions, including what actions can be executed.
This declaration of required code, which can be found within the Google Play store, is not the case when exploiting StrandHogg 2.0.
As no external configuration is required to execute StrandHogg 2.0, it allows the hacker to further obfuscate the attack, as code obtained from Google Play will not initially appear suspicious to developers and security teams.
Malware that exploits StrandHogg 2.0 will also be harder for anti-virus and security scanners to detect and, as such, poses a significant danger to the end-user.
Promon predicts that attackers will look to utilise both StrandHogg and StrandHogg 2.0 together because both vulnerabilities are uniquely positioned to attack devices in different ways, and doing so would ensure that the target area is as broad as possible.
Likewise, many of the mitigations that can be executed against StrandHogg do not apply to StrandHogg 2.0 and vice-versa.
StrandHogg 2.0 exploits do not impact devices running Android 10. However with a significant proportion of Android users reported to still be running older versions of the OS, a large percentage of the global population is still at risk.
According to data from Google, as of April 2020, 91.8% of Android active users worldwide are on version 9.0 or earlier: Pie (2018), Oreo (2017), Nougat (2016), Marshmallow (2015), Lollipop (2014), KitKat (2013), Jellybean (2012) and Ice Cream Sandwich (2011).
Tom Lysemose Hansen, CTO and founder of Promon comments: “We see StrandHogg 2.0 as StrandHogg’s even more evil twin.
They are similar in the sense that hackers can exploit both vulnerabilities in order to gain access to very personal information and services, but from our extensive research, we can see that StrandHogg 2.0 enables hackers to attack much more broadly while being far more difficult to detect.
Attackers looking to exploit StrandHogg 2.0 will likely already be aware of the original StrandHogg vulnerability and the concern is that, when used together it becomes a powerful attack tool for malicious actors.
Android users should update their devices to the latest firmware as soon as possible in order to protect themselves against attacks utilising StrandHogg 2.0.
Similarly, app developers must ensure that all apps are distributed with the appropriate security measures in place in order to mitigate the risks of attacks in the wild.
Promon CEO Gustaf Sahlman adds: “We remain in constructive dialogue with Google, which has acknowledged the severity of StrandHogg 2.0 and is set to roll out a fix to the general public in May.
Promon has once again discovered a potentially catastrophic Android vulnerability, which thanks to our researchers will be fixed before it could be used by hackers to cause all sorts of distress for people and businesses around the world.”
Vulnerability Disclosure Timeline
Promon’s announcement of StrandHogg 2.0 was coordinated with Google, which was notified of the vulnerability on 4 December 2019, allowing more than reasonable time to release a fix.
Google, has rolled out a patch to Android ecosystem partners in April 2020, with a fix security patch (Android versions 8.0, 8.1, and 9) set to be rolled out to the general public in May 2020.
The vulnerability has been given the Common Vulnerability and Exposures (CVE) number CVE-2020-0096.
Q&A
We have not observed any real-life malware utilising the StrandHogg 2.0 vulnerability.
Google has rolled out a patch to Android ecosystem partners in April 2020, with a fix (Android versions 8.0, 8.1, and 9) set to be rolled out to the general public in May 2020. The vulnerability has been given the Common Vulnerability and Exposures (CVE) number CVE-2020-0096.
This vulnerability can be exploited without root access.
- Listening to the user through the microphone
- Take photos through the camera
- Read and send SMS messages
- Make and/or record phone conversations
- Phish login credentials
- Get access to all private photos and files on the device
- Get location and GPS information
- Get access to the contacts list
- Access phone logs
Most apps. As with the predecessor, StrandHogg (1.0), most apps are vulnerable by default.
The vulnerability affects devices running Android 9.0 and below. StrandHogg 2.0 exploits do not impact devices running Android 10.
Google was notified of the vulnerability on 4 December 2019, allowing more than reasonable time to release a fix.
Android users should update their devices to the latest firmware as soon as possible in order to protect themselves against attacks utilising StrandHogg 2.0. Similarly, app developers must ensure that all apps are distributed with the appropriate security measures in place in order to mitigate the risks of attacks in the wild.
App providers can also download our technical report for mitigation recommendations & POC.
Both vulnerabilities have been named by Promon as ‘StrandHogg’, old Norse for the Viking tactic of raiding coastal areas to plunder and hold people for ransom.